3 Views
• 27/12/22
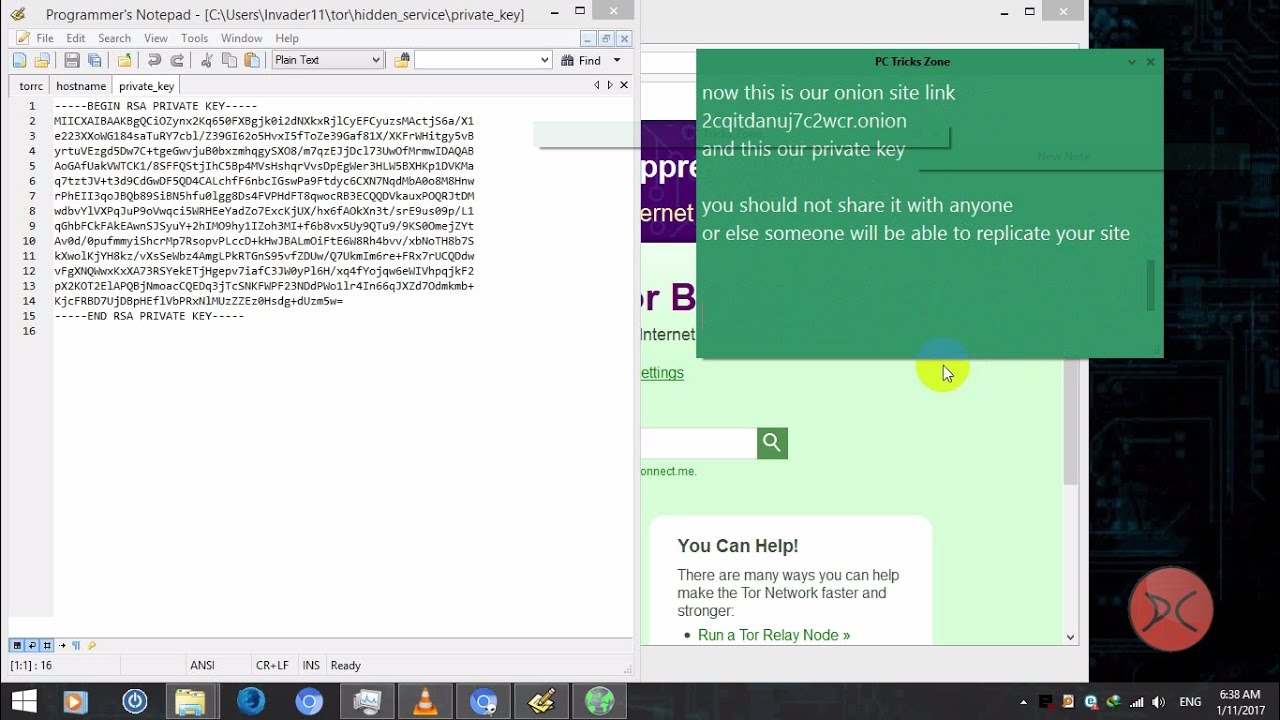
Wireless attacks using rogue access points pushed into browser exploitation framework to get usernames and passwords. Video is strictly for educational purposes.
Ethical Hacker | Penetration Tester | Cybersecurity Consultant
About The Trainer:
Loi Liang Yang
Certified Information Systems Security Professional
Certified Ethical Hacker
CompTIA Security+
Social networks:
http://www.loiliangyang.com
http://www.facebook.com/Loiliangyang/
http://www.instagram.com/loiliangyang/
http://www.linkedin.com/in/loiliangyang/
Subscribe now:
Learn about ethical hacking
Learn about wireless hacking
Learn about android hacking
Learn about penetration testing
Learn about linux
Show more




















SORT BY-
Top Comments
-
Latest comments